COMPUTER HACKERS AND CRACKERS
Hacker : Hacker is a term used by some to mean “a clever programmer” and by others, especially those in popular media, to mean “someone who tries to break into computer systems”. A Hacker can be a expert programmer.
Cracker : Malicious Hacker known as cracker, refer to those who break into computers without authorization.
Hacking : Hacking is unauthorized use of computer and network resources.(The term “hacker” originally meant a very gifted programmer. In recent years though, with easier access to multiple systems, it now has negative implication).
Types of Hackers
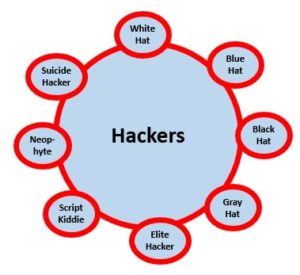
- White Hat : A white hat hacker breaks security for non-malicious reasons, for instance testing their own security system. ‘White hat’ hacker is called an ethical hacker. The International Council of Electronic Commerce Consultants, also known as the EC-Council has developed certifications, courseware, classes, and online training covering the diverse arena of Ethical Hacking.
- Blue Hat : A blue hat hacker is someone outside computer security consulting firms who is used to bug test a system prior to its launch, looking for exploits so they can be closed. Microsoft also uses the term Blue Hat to represent a series of security briefing events.
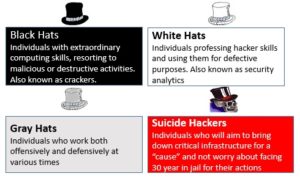
- Black Hat : A Black Hat Hacker is a hacker who violates computer security for little reason beyond maliciousness or for personal gain.Black Hat Hackers break into secure networks to destroy data or make the network unusable.
- Grey Hat : A grey hat hacker is a combination of a Black Hat and a White Hat Hacker. A Grey Hat Hacker may surf the internet and hack into a computer system for the sole purpose of notifying the administrator that their system has been hacked, for example.Then they may offer to repair their system for a small fee.
- Elite Hacker : A social status among hackers, elite is used to describe the most skilled. Newly discovered exploits will circulate among these hackers. Elite group such as Masters of Deception conferred a kind of credibility on their members.
- Script Kiddie : A script kiddie is a non-expert who breaks into computer systems by using pre-packaged automated tools written by others, usually with little understanding of the underlying concepts-hence the term script(i.e. a prearranged plan or set of activities) kiddie(immature).
- Neophyte : A neophyte, “n00b” or “newbie” is someone who is new to hacking or phreaking and has almost no knowledge or experience of the workings of technology and hacking.
- Suicide Hackers : Individuals who will aim to bring down critical infrastructure for a “cause” and not worry about facing 30 years jail for their actions.
Difference between Hackers and Crackers :

Hackers : A Hacker is a person who is extremely interested in exploring the the things and recondite working of any computer system or networking system. Most often, hackers are expert programmers. These are also called Ethical Hackers or white hat hackers. The technique they use is called ethical hacking.
Ethical Hacking means you think like Hackers. First you hack systems and find the loop holes and then you try to correct those loop holes.These type of hackers protect the cyber world from every possible threat and fix potential future security loop holes. These people are also called the “GURU’s” of Computer Security.
Crackers : Crackers or Black Hat hackers are also called cheaters or simply criminals. They are called criminals because they intend to cause harm to security, stealing very useful data and using it in wrong ways. Phishers, who steal account information and credit card numbers, also fall into this category.
Thanks you and All the best!
You can join or visit at Facebook Page or Twitter for always keep in touch with further updates.
Read more articles….
| Computer Security | Data Communication |
|---|
